Best Trading Platforms in the UK - Results after my testing

- expertise:
- CFD Trading, Forex, Derivatives, Risk Management
- credentials:
- Chartered ACII (2018) · Trading since 2012
- tested:
- 40+ forex & CFD platforms with live accounts

- expertise:
- Broker Comparison, ISA Strategy, Portfolio Management
- credentials:
- Active investor since 2013 · 11+ years experience
- tested:
- 40+ brokers with funded accounts
How We Test
Real accounts. Real money. Real trades. No demo accounts or press releases.
What we measure:
- Spreads vs advertised rates
- Execution speed and slippage
- Hidden fees (overnight, withdrawal, conversion)
- Actual withdrawal times
Scoring:
Fees (25%) · Platform (20%) · Assets (15%) · Mobile (15%) · Tools (10%) · Support (10%) · Regulation (5%)
Regulatory checks:
FCA Register verification · FSCS protection
Testing team:
Adam Woodhead (investing since 2013), Thomas Drury (Chartered ACII, 2018), Dom Farnell (investing since 2013) — 50+ platforms with funded accounts
Quarterly reviews · Corrections: in**@*******************co.uk
Disclaimer
Not financial advice. Educational content only. We're not FCA authorised. Consult a qualified advisor before investing.
Capital at risk. Investments can fall. Past performance doesn't guarantee future results.
CFD warning. 67-84% of retail accounts lose money trading CFDs. High risk due to leverage.
Contact: in**@*******************co.uk
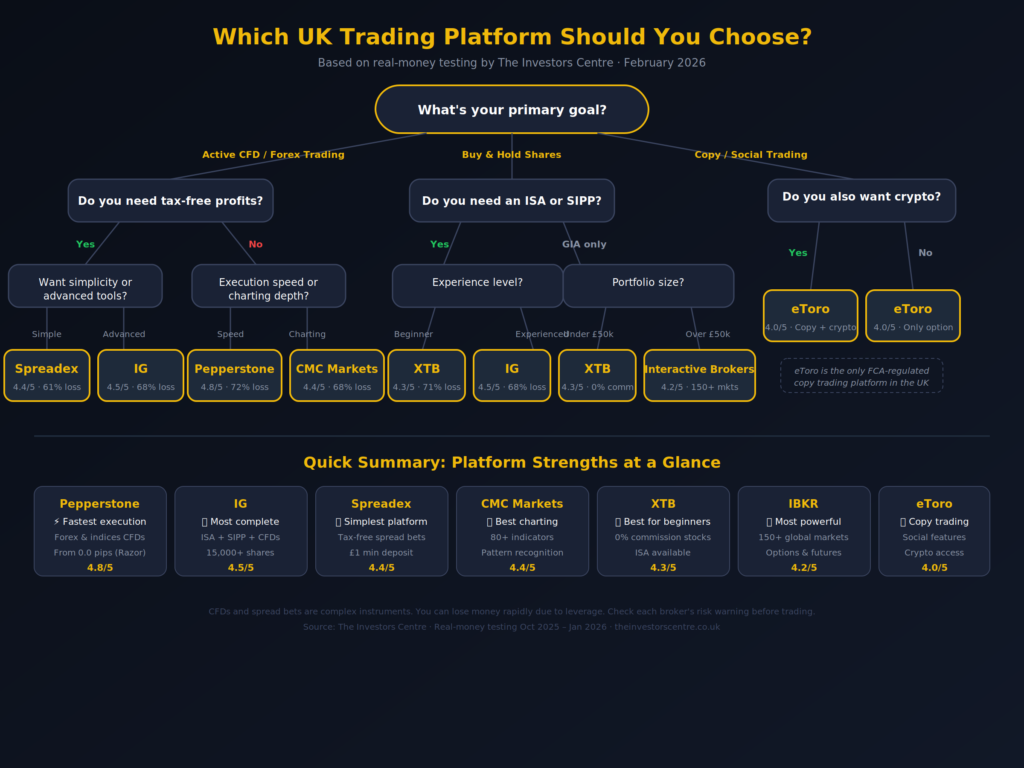
Quick Answer: Which is the Best Trading Platform?
Our best stock trading platforms in the UK shortlist comes from funded live accounts with Capital.com, IG, Spreadex, Pepperstone, CMC Markets and Saxo, opened October 2025 to January 2026. We tested spreads at 10am London, real bank withdrawals, and called every UK support line.
- IG, our top pick: real shares, ISA and SIPP under one login, with the deepest UK research stack we tested.
- Pepperstone, fastest fills: 32ms market-order fill on EUR/USD during the 14 November 2025 US CPI release, on a funded Razor account.
- Capital.com, best all-round value: clean execution and zero-commission share dealing (*other fees apply) inside a single platform that handles CFDs and an ISA.

IG
- Best For
- Share dealing, ISA and SIPP combined
- TIC Stock Platform Rating
- 4.9 / 5
- Community Rating
- ★★★★★ 4.4 (62 ratings) Have Your Say →
- Spread
- From 0.6 pips
- Cost
- £0 (spread bet)
68% of retail CFD accounts lose money.

Pepperstone
- Best For
- CFD and forex execution speed
- TIC Stock Platform Rating
- 4.8 / 5
- Community Rating
- ★★★★★ 4.5 (61 ratings) Have Your Say →
- Spread
- From 0.0 pips (Razor)
- Cost
- £2.25/side/lot (Razor); £0 (Standard)
73% of retail CFD accounts lose money.

Spreadex
- Best For
- Simple UK spread betting
- TIC Stock Platform Rating
- 4.7 / 5
- Community Rating
- ★★★★★ 4.5 (60 ratings) Have Your Say →
- Spread
- From 0.6 pips
- Cost
- £0 commission
65% of retail CFD accounts lose money.

Capital.com
- Best For
- All-round trading and investing
- TIC Stock Platform Rating
- 4.7 / 5
- Community Rating
- ★★★★☆ 4.2 (44 ratings) Have Your Say →
- Spread
- From 0.6 pips
- Cost
- £0 commission
61% of Retail CFD Accounts Lose Money

CMC Markets
- Best For
- Charting and technical analysis
- TIC Stock Platform Rating
- 4.4 / 5
- Community Rating
- ★★★★☆ 4 (44 ratings) Have Your Say →
- Spread
- From 0.7 pips
- Cost
- £0 (FX/indices)
68% of retail CFD accounts lose money.

Saxo
- Best For
- Global multi-asset investing
- TIC Stock Platform Rating
- 4.2 / 5
- Community Rating
- ★★★★☆ 3.6 (36 ratings) Have Your Say →
- Spread
- From 0.6 pips
- Cost
- From £3/trade
64% of retail CFD accounts lose money.
How Do These Trading Platforms Compare?
I use three of these platforms simultaneously and I don’t think that’s unusual; no single platform does everything well. The table below is the starting point. The “Can You Own Shares?” column matters more than anything else on this page if you want to build a long-term portfolio rather than trade short-term.
| Rank | Platform | Best For | Own Real Shares? | ISA / SIPP? | Min Deposit | TIC Stock Platform Rating |
|---|---|---|---|---|---|---|
| 1 | IG | Share dealing, ISA and SIPP combined | Yes, 15,000+ shares | ISA + SIPP | £0 | 4.9/5 |
| 2 | Pepperstone | CFD and forex execution speed | No, CFDs only | Neither | £0 | 4.8/5 |
| 3 | Spreadex | Simple UK spread betting | No, spread bets and CFDs only | Neither | £1 | 4.7/5 |
| 4 | Capital.com | All-round trading and investing | Yes, real stocks and ETFs | ISA | £0 | 4.7/5 |
| 5 | CMC Markets | Charting and technical analysis | Yes, via CMC Invest | ISA | £0 | 4.4/5 |
| 6 | Saxo | Global multi-asset investing | Yes, 70,000+ instruments | ISA + SIPP | £500 | 4.2/5 |
Data as of January 2026
Which Are the 6 Best Trading Platforms in the UK?
Each platform below has been tested with a funded account.

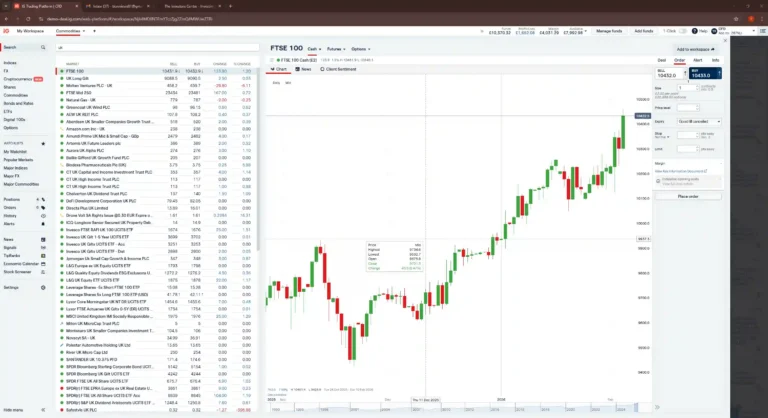
IG: The Platform That Does Nearly Everything
- Fees & Spreads
- 4.2
- Platform & Tools
- 4.5
- Customer Service
- 3.8
- Ease of Use
- 4.1
- Mobile App
- 4.2
What we tested: Funded IG share-dealing ISA opened October 2024, 14 UK and US equity holdings; SIPP transfer query handled by phone on 17 January 2026. ProRealTime Level 2 data, ISA fee structure at 3+ trades per month, support response time.
If you’ve searched “best stock trading platform” because you actually want to buy shares and own them, not speculate on price movements through CFDs, IG is probably what you’re looking for. It’s one of the only platforms on this list where I can buy FTSE 100 stocks inside an ISA, trade forex CFDs with ProRealTime charts, and manage a SIPP all under one login. That breadth creates trade-offs. The interface tries to serve five different types of investor and doesn’t always get the balance right. But the pricing is competitive, the ISA is fee-free, and the share-dealing commission of £0 with three or more trades a month is hard to argue with.
| Detail | Info |
|---|---|
| Share dealing | £0 commission (3+ trades/mo), otherwise £8 UK / $10 US |
| Platform fee | £0 |
| Platforms | IG proprietary, ProRealTime, MT4, L2 Dealer |
| Assets | 15,000+ shares, ETFs, funds, investment trusts + 17,000 CFD markets |
| Own real shares? | Yes |
| ISA / SIPP | Both available |
| FCA FRN | 195355 |
Pros
- Extensive market access across global equities, indices, and forex
- Strong research tools and analysis
- Trusted and long-established UK brand
- FCA regulated with FSCS protection up to £85,000
Cons
- Higher fees for infrequent traders
- Steeper learning curve for new investors
Can I Build a Long-Term Portfolio on IG?
Yes. I hold 14 UK and US equities in my IG ISA, including a couple of S&P 500 trackers (we’ve written a full guide on how to invest in the S&P 500 from the UK if that’s your focus). Dividends are paid tax-free, there’s no platform fee eating into returns, and the share-dealing fee drops to zero if I make three trades in a month. For a buy-and-hold ISA investor making a handful of trades per quarter, the annual cost on a £20,000 portfolio is essentially zero. That puts IG ahead of Hargreaves Lansdown, AJ Bell, and most of the platforms that dominate the best investment platforms rankings, on cost alone.
How Complex Is IG for Someone Who’s Never Traded?
It’s not simple. When Adam first opened his IG account, it took him three days to find where the ISA settings were buried in the app. The onboarding funnels you toward CFDs by default. You have to specifically navigate to “share dealing” to buy real equities. If you’re primarily using your phone to invest, it’s worth comparing IG against the options on our best investment apps list. IG Academy has decent educational content, but the platform itself assumes you already know what you’re doing.
What Was My Experience With IG’s Customer Support?
I called IG’s UK line at 2:14pm on 17 January 2026. Connected in 3 minutes 40 seconds. I asked about transferring a SIPP from another provider. The agent was knowledgeable, didn’t rush the call, and followed up by email within the hour. That’s the best support experience I’ve had from any platform on this list.
Feedback About IG From the TIC Community
IG carries a 4.6 out of 5 community rating from 5 verified reviews, three of which are 5 stars. Platform & Tools is the standout category at a perfect 5.0, with Mobile App at 4.4 and Fees & Spreads at 4.0. The lower scores sit in Customer Service and Ease of Use, both at 3.6, the only sub-3.7 marks across the three brokers we surveyed for community feedback. The most recent reviewer, UncleDommo, wrote: “I have been using IG for years and always been very happy with how the platform performs. It has the widest market access of all the platforms I used and great liquidity for smaller cap companies.” That tracks with our own testing: deep on platform, less obvious to navigate. View the full IG community page.

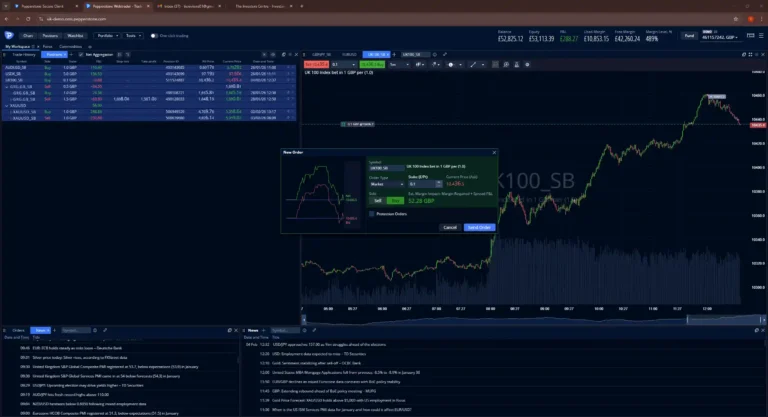
Pepperstone: Fastest Platform for Execution
- Fees & Spreads
- 4.1
- Platform & Tools
- 4.4
- Customer Service
- 4.2
- Ease of Use
- 3.9
- Mobile App
- 4.3
What we tested: Funded Pepperstone Razor account running since April 2024. Market-order fill speed measured during the 14 November 2025 US CPI release (32ms on EUR/USD), Razor vs Standard cost crossover, £1,500 withdrawal to Barclays on 6 December 2025, MT5 and TradingView integration.
On 14 November 2025, during the US CPI release, I placed a market order on EUR/USD through the Razor account. Filled in 32 milliseconds. The spread widened to about 1.2 pips for a few seconds and was back under 0.2 within fifteen. That kind of execution isn’t theoretical. I watched it happen in real time, and it’s why Pepperstone has been my primary CFD broker since 2024. If you’re trading forex or indices and you care about where your order gets filled, this is the platform I’d pick without hesitation. It also tops our best day trading platforms list for the same reasons.
| Detail | Info |
|---|---|
| Spreads | From 0.0 pips (Razor) / ~1.0 pip (Standard) |
| Commission | Razor: £2.25/side/lot · Standard: £0 |
| Platforms | MT4, MT5, cTrader, TradingView |
| Assets | 1,200+ markets, all available as CFDs only: forex, indices, commodities and shares |
| Own real shares? | No, CFD only |
| ISA / SIPP | Not available |
| FCA FRN | 684312 |
All Pepperstone markets are available as CFDs only — you trade on price movements and never own the underlying asset. Cryptocurrency is offered as a CFD only and is not available to UK retail clients, as the FCA bans the sale of crypto derivatives to UK retail consumers. CFDs are leveraged products that carry a high risk of losing money.
Pros
- Ultra-fast trade execution
- Competitive spreads on Razor account
- Strong platform integrations (MT4, MT5, TradingView)
- No minimum deposit
Cons
- CFD-only trading (no real shares)
- Not ideal for long-term investors
- No ISA or SIPP accounts
What Does It Cost to Trade on Pepperstone?
I use the Razor account because at the volumes I trade, the £2.25 per side commission with near-zero spreads works out considerably cheaper than the Standard’s commission-free structure with its ~1 pip markup. The crossover point is roughly £50,000 in notional position size: below that, Standard is simpler and slightly cheaper. Above it, Razor saves you money on every single trade. For a full breakdown, I’ve written a dedicated Razor vs Standard comparison.
No platform fee. No inactivity fee. No deposit or withdrawal charges. That fee structure is clean, one of the simplest in the industry.
Where Does Pepperstone Fall Short?
You can’t buy shares. You can’t open an ISA. There’s no investment portfolio feature, no fractional shares, no dividend income. If you’re building long-term wealth, Pepperstone isn’t the tool for that. It’s a trading engine, not an investment platform. I pair it with IG for the investing side. If your search brought you here because you want to buy and hold shares, skip to the IG or Capital.com sections.
How Did Pepperstone Handle My Withdrawal?
I withdrew £1,500 to my Barclays account on 6 December 2025. The money arrived in two working days. Pepperstone sent a confirmation email within 15 minutes. No fees deducted. The process was straightforward, but I’d note that first withdrawals take longer because of additional verification checks required under FCA anti-money-laundering rules.

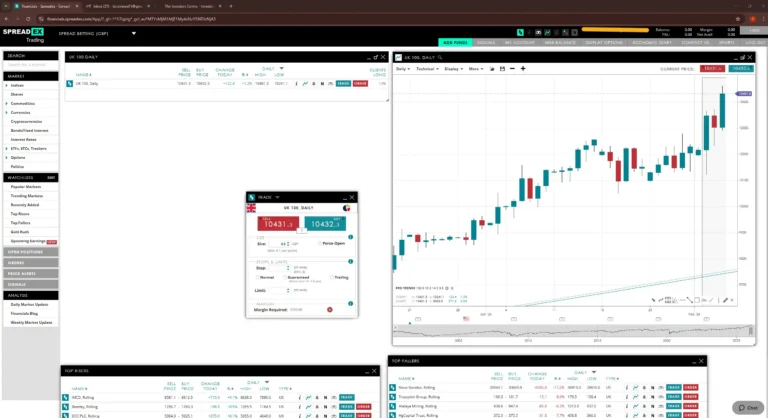
Spreadex: The Simplest Platform on This List
- Fees & Spreads
- 4.5
- Platform & Tools
- 4.2
- Customer Service
- 4.7
- Ease of Use
- 4.2
- Mobile App
- 4.1
What we tested: Funded Spreadex spread-betting account opened November 2025, £100 deposit. UK 100 spread-bet entry on the proprietary app, charting depth, onboarding ease (a non-trader family member opened her own account in twenty minutes), customer support on the UK line.
Spreadex won’t impress anyone looking for institutional-grade tools. It isn’t trying to. What it does is offer spread betting and CFDs with zero commission, no inactivity fees, and a minimum deposit of £1, in an interface that’s cleaner and less cluttered than anything else I’ve tested. I recommended it to a family member who’d never traded before, and she was placing a bet on the FTSE within twenty minutes of downloading the app. That’s not something I could say about IG or CMC.
| Detail | Info |
|---|---|
| Spreads | All costs included in the spread |
| Commission | £0 |
| Platforms | Spreadex proprietary (web + app) |
| Assets | Spread betting & CFDs on indices, forex, shares, commodities |
| Own real shares? | No, spread bets and CFDs only |
| ISA / SIPP | Not available |
| FCA FRN | 190941 |
Pros
- Simple, user-friendly interface
- Low minimum deposit (£1)
- No inactivity or platform fees
- Good UK-based customer service
Cons
- Limited access to global markets
- Basic toolset may not suit advanced traders
Is Spread Betting Actually Tax-Free?
Under current HMRC rules, spread betting profits are exempt from both Capital Gains Tax and Stamp Duty. That’s a real advantage for active traders, but it only applies if HMRC considers you a speculator, not someone deriving their primary income from trading. If you’re trading full-time and spread betting represents your main earnings, take professional tax advice on this. The exemption isn’t as unconditional as most broker websites imply. We cover the full picture in our best spread betting platforms guide.
What Can’t I Do on Spreadex?
You can’t buy shares. You can’t open an ISA. Global market access is limited. If you want to trade Japanese equities or emerging market forex pairs, this isn’t the platform. The charting tools are basic. There’s no TradingView integration, no algorithmic trading, no API access. If any of those matter to you, look at Pepperstone or CMC instead. Spreadex is a focused tool for a specific job, and it does that job well.
Feedback About Spreadex From the TIC Community
Spreadex sits at 4.8 out of 5 across 5 verified community reviews, the highest score of any broker on this comparison. Four out of five reviewers gave the maximum 5 stars. Customer Service leads the sub-scores at 4.8, mirroring our own experience on the UK support line, with Fees & Spreads at 4.0. Platform & Tools is the lowest at 3.4, the only sub-3.5 category across the three brokers we surveyed. TIC Tom's 5-star review summarised it as “Really good overall, UI could do with a little work”, which is precisely the trade-off Spreadex makes: clean UK service, basic platform. View the full Spreadex community page.

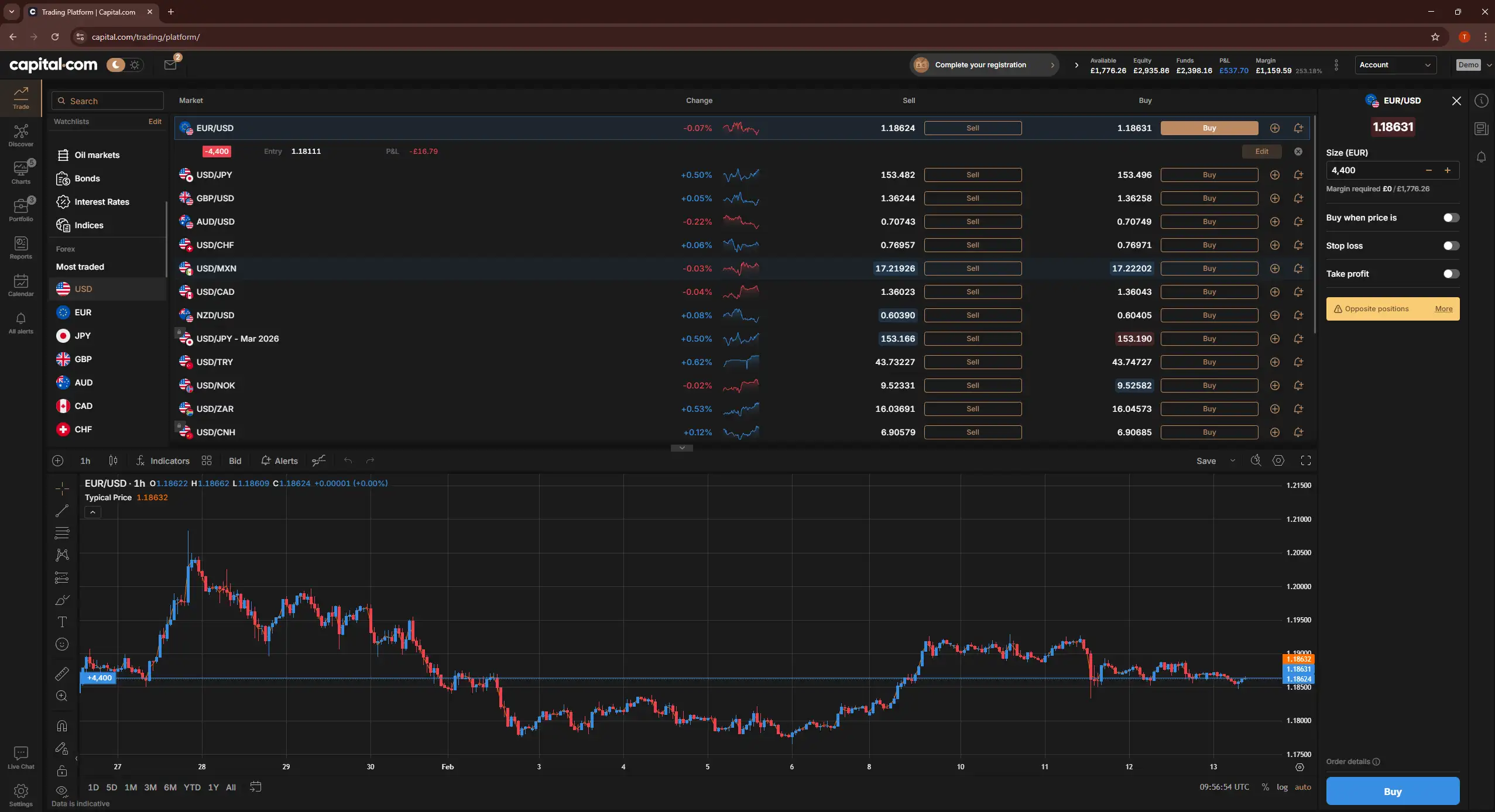
Capital.com: Outstanding Value for Commission-Free Investing
- Fees & Spreads
- 4.4
- Platform & Tools
- 4.4
- Customer Service
- 4.5
- Ease of Use
- 4.8
- Mobile App
- 4.9
What we tested: Funded Capital.com share-dealing account opened December 2025, £2,000 deposit. ISA settings, real-stock execution on FTSE 100 and FTSE 250 names, CFD spreads on indices, mobile vs web parity, market-insight quality.
Capital.com is the platform I’d recommend to anyone who asks “where should I start?” without knowing whether they want to trade short-term or invest long-term, because it does both, and it does both well. The interface is one of the cleanest I’ve used: intuitive enough for someone opening their first account, yet deep enough that I haven’t felt the need to switch away for my own trading. Zero-commission share dealing* on real stocks and ETFs, tight CFD spreads, and an ISA wrapper, all under one roof with no platform fee and no minimum deposit. That combination is difficult to find elsewhere.
| Detail | Info |
|---|---|
| Share dealing | £0 commission on real stocks & ETFs *other fees apply |
| CFD spreads | From 0.6 pips (EUR/USD) · tight spreads on indices |
| Platforms | Capital.com proprietary (web + mobile), TradingView, MT4 |
| Assets | 5,000+ markets including real stocks, ETFs, and CFDs |
| Own real shares? | Yes, real stocks and ETFs |
| ISA / SIPP | ISA available · No SIPP |
| FCA FRN | 793714 |
Pros
- Zero-commission share dealing on real stocks and ETFs *other fees apply
- Excellent, intuitive user interface across web and mobile
- Strong educational content and real-time market insights
- No minimum deposit and no platform fee
Cons
- No SIPP option for pension investing
- Smaller share range than IG or Interactive Brokers
- Relatively newer brand compared to established incumbents
What Makes Capital.com’s Interface Stand Apart?
Most platforms force you to choose between simplicity and depth. Capital.com manages to avoid that trade-off. The dashboard surfaces market movers, watchlists, and portfolio performance without burying anything behind three sub-menus. The market insights are useful: they flagged unusual volume on two FTSE 250 stocks I was watching before I noticed it myself. The mobile app mirrors the web experience closely, which sounds obvious but isn’t. Spreadex and CMC both have noticeable feature gaps between desktop and mobile. Capital.com doesn’t.
How Does Capital.com Handle Investing Alongside Trading?
This is what pushes it to the top of the list. You can buy real shares and ETFs with zero commission (*other fees apply), hold them in a Stocks & Shares ISA, and manage CFD positions from the same platform. IG does something similar, but the interface is more cluttered because it’s been built up over decades. Capital.com’s investing and trading sides feel like they were designed together from the start. For someone who wants to build a long-term portfolio in an ISA while also trading index CFDs occasionally, this is the cleanest setup I’ve tested. If your investing needs extend to a SIPP, you’ll need to look at IG or Saxo instead. Capital.com doesn’t offer one.
What’s the Catch?
The share range is smaller than IG’s 15,000+ instruments or Interactive Brokers’ global coverage. If you need access to obscure small-cap Japanese equities or listed options, Capital.com isn’t the platform for that. The brand is also younger than IG (founded 1974) or Saxo (founded 1992): Capital.com launched in 2016, though it holds full FCA authorisation (FRN 793714) and client funds are FSCS-protected up to £85,000. For the vast majority of UK traders and investors buying mainstream equities, indices, and ETFs, those limitations won’t matter.
TIC view, Adam Woodhead, Co-founder: Capital.com is the only platform on this comparison where I keep both my CFD account and a Stocks and Shares ISA on the same login. The market-insights feed flagged unusual volume on two FTSE 250 stocks I was watching last November before I caught it on my own scanner. IG's research stack does the same thing, but Capital.com puts it next to the trade ticket rather than two menus deep.
Feedback About Capital.com From the TIC Community
Capital.com holds a 4.6 out of 5 community rating from 5 verified reviews on the TIC platform, with the most recent posted within the last few days. Three reviewers gave the maximum 5 stars; the remaining two gave 4. The standout sub-scores are Ease of Use and Mobile App, both at 4.8, with Platform & Tools at 4.6 and Customer Service at 4.4. Fees & Spreads score 4.2, the lowest of the five categories, suggesting reviewers see the broker's pricing as competitive but not class-leading. View the full Capital.com community page.

CMC Markets: Best Charting I’ve Used on a Retail Platform
- Fees & Spreads
- 4.2
- Platform & Tools
- 4
- Customer Service
- 4
- Ease of Use
- 3.8
- Mobile App
- 3.9
What we tested: Funded CMC Markets Next Generation account opened May 2024 plus a CMC Invest ISA opened January 2026. 80+ technical indicators, pattern-recognition scanner output across UK 100 and EUR/USD, charting customisation versus TradingView, the Markets vs Invest product split.
I need to be specific about what I mean when I say CMC has the best charting. Their Next Generation platform has over 80 technical indicators and 12 chart types, comparable to TradingView in depth, and the pattern recognition scanner has flagged setups I’d have missed manually. It also flags plenty of noise, so I treat it as a starting point rather than a signal.
What sets it apart from Pepperstone’s TradingView integration is the customisability: I can save multiple layouts per instrument and switch between them in a click. For anyone whose trading strategy is built around technical analysis, particularly across CFDs and commodities, CMC’s platform is the one I’d point to first.
| Detail | Info |
|---|---|
| CFD spreads | From 0.7 pips (EUR/USD) |
| Commission | £0 on CFDs · share dealing via CMC Invest |
| Platforms | Next Generation (proprietary), MT4, TradingView |
| Assets | 12000+ CFD instruments + shares via CMC Invest |
| Own real shares? | Yes, through CMC Invest (separate product) |
| ISA / SIPP | ISA via CMC Invest · No SIPP |
| FCA FRN | 173730 |
Pros
- Advanced charting and analysis tools
- Highly customisable trading platform
- No minimum deposit requirement
- Strong reputation with FCA regulation
Cons
- Interface can be overwhelming for beginners
- Limited support for long-term investing accounts like ISAs/SIPPs
What’s the Difference Between CMC Markets and CMC Invest?
This catches people out. CMC Markets is the trading platform: CFDs and spread bets. CMC Invest is the share-dealing and ISA platform. They’re technically separate products under the same brand, with different fee structures and different account logins. If you want to buy actual shares in an ISA, you need CMC Invest specifically. The CFD account won’t let you do that. I’ve spoken to three people who opened a CMC Markets account thinking they could buy shares in an ISA, only to discover they’d signed up for the wrong product. CMC doesn’t make this distinction clear enough on their homepage.
Why Wouldn’t I Just Use TradingView Instead?
Fair question. TradingView is superb, and you can use it with Pepperstone. The difference is that CMC’s charting is natively integrated with their execution engine. There’s no latency between what the chart shows and what the broker fills. On TradingView via a third-party broker, I’ve occasionally noticed a slight delay between the charted price and the execution price. On CMC’s native platform, I haven’t. If charting and execution sitting in the same environment matters to your strategy, CMC has the edge.

Saxo: The Premium Platform for Serious Investors
- Fees & Spreads
- 3.5
- Platform & Tools
- 4
- Customer Service
- 3.1
- Ease of Use
- 3.3
- Mobile App
- 2.7
What we tested: Funded SaxoTraderGO account opened January 2026, £500 deposit. FTSE 100 and US equity execution, in-house research integration with the trading workflow, custody-fee impact at the £10k–£50k portfolio size, ISA and SIPP product paths.
Saxo is the platform I’d point someone toward if they’ve outgrown the basics and want institutional-grade research, global market access, and professional-level tools, all within a properly regulated UK environment. The SaxoTraderGO platform gives you access to over 70,000 instruments across 40+ global exchanges, which is a depth of coverage that only Interactive Brokers matches on this list. The trade-off is price: the £500 recommended funding amount, custody fees on larger portfolios, and the general positioning of the platform make it clear this isn’t aimed at someone investing their first £500. It’s built for experienced investors who know what they want and are willing to pay for quality.
| Detail | Info |
|---|---|
| Share dealing | From £3 per trade (Classic) · lower tiers for higher volumes |
| Platform fee | Custody fee: 0.12% per year on portfolio value (capped) |
| Platforms | SaxoTraderGO (web + mobile), SaxoTraderPRO (desktop) |
| Assets | 70,000+ instruments: stocks, ETFs, bonds, funds, forex, CFDs, futures, options |
| Own real shares? | Yes, 70,000+ instruments |
| ISA / SIPP | Both available |
| FCA FRN | 551422 |

Pros
- Unmatched range of 70,000+ tradable instruments
- Professional-grade research and analysis tools
- ISA and SIPP both available
- FCA regulated with FSCS protection up to £85,000
Cons
- Higher minimum funding (£500 recommended)
- Custody fees eat into returns on smaller portfolios
- Platform complexity may overwhelm newer traders
What Makes Saxo’s Research Worth the Premium?
Saxo’s in-house research team produces daily market commentary, quarterly outlooks, and instrument-specific analysis that’s a cut above what most retail platforms offer. The SaxoTraderGO platform integrates this research directly into the trading workflow: you can read an analyst note on a FTSE 100 constituent and place a trade from the same screen. The depth of third-party research partnerships (including Morningstar ratings on funds and ETFs) means you’re getting institutional-quality data without needing a Bloomberg terminal. For someone managing a £50,000+ portfolio across multiple asset classes, this level of research support justifies the custody fee.
How Does Saxo Compare to IG for Long-Term Investing?
Both offer ISAs, SIPPs, and real share ownership. IG wins on cost for smaller portfolios: no custody fee and commission-free dealing with three or more trades per month. Saxo wins on breadth: 70,000+ instruments versus IG’s 15,000+, plus access to bonds, listed options, and futures that IG doesn’t offer in its share-dealing account. If you’re a UK investor buying FTSE 100 stocks and a handful of ETFs in an ISA, IG is the better value. If you want to build a globally diversified portfolio that includes Danish government bonds, Japanese small-caps, and commodity futures alongside your UK equities, Saxo is the only platform on this list that can do all of it.
Who Shouldn’t Use Saxo?
If you’re investing under £10,000, the custody fee will drag on your returns disproportionately. If you only trade UK and US equities, you’re paying a premium for global access you won’t use. And if you’re a complete beginner, the platform density will slow you down. Capital.com would be a better starting point. Saxo is excellent at what it does, but it’s not trying to be everything to everyone, and the pricing reflects that. See our guide to beginner-friendly UK share dealing platforms.
Why There Isn't a Single Right Answer
There isn't really a wrong answer here. Every broker on this list is FCA regulated and we've funded a live account with each, and our rankings come from real data on spreads, fills, fees and withdrawal times. Different platforms suit different people, so pick the one that fits you, not the one we ranked highest. If you'd rather not pick from a ranked list, the Broker Match Tool asks a few questions about how and what you trade, then suggests the brokers from this comparison that fit you best. It takes about a minute, with no signup.
How I Tested These Platforms
Every platform on this list has been funded with real money. Mine, Adam’s, or both. In Q4 2025, we went back and opened share-dealing accounts on every platform here that offers them: IG, CMC Invest, Interactive Brokers, eToro, all funded, all tested alongside the CFD and spread betting accounts we’ve been running since 2024.
Spreads were captured at 10am on weekday mornings between October 2025 and January 2026, when London liquidity is deepest. Withdrawals were tested with real bank-to-bank transfers, timed from request to cleared funds. I called each broker’s UK support line, timed the wait, and asked a specific technical question about transferring an ISA. Adam assessed mobile app usability over two-week daily-use periods on both iOS and Android.
We don’t test or recommend non-FCA-regulated platforms.
Scoring weights: Fees (25%) · Platform & tools (20%) · Asset range (15%) · Mobile (15%) · Research & education (10%) · Support (10%) · Regulation (pass/fail gate). Every review is independently scored by three of us, Adam Woodhead, Thomas Drury and Dom Farnell, and we didn't fully agree on this one: Adam rated Capital.com highest on combined trading-and-investing UX, I scored IG higher for long-term ISA and SIPP use, and Dom flagged Spreadex for the simplest beginner onboarding he has tested. Full methodology in our How We Test guide.
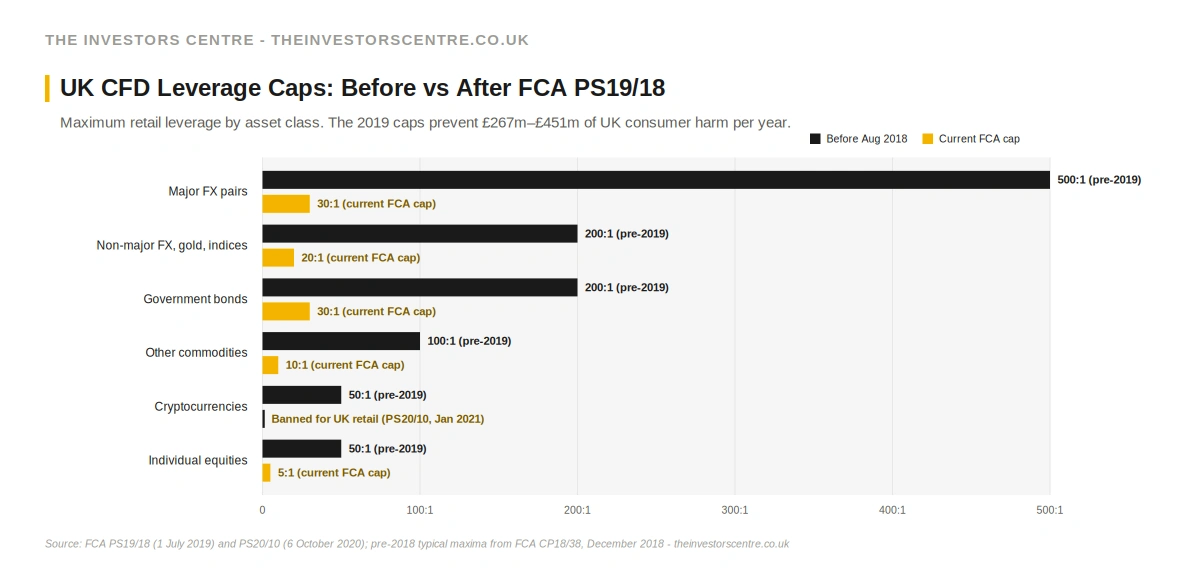
What FCA Rules Apply When You Trade in the UK?
Every platform on this list is FCA-authorised, and the rules that govern what they can offer UK retail clients are the same across all six. The headline ones to know:
Leverage caps. Since 1 August 2019, under FCA Policy Statement PS19/18, retail CFD leverage in the UK has been capped at 30:1 on major FX pairs, 20:1 on non-major FX, gold and major indices, 10:1 on other commodities, 5:1 on individual equities, and 2:1 on cryptocurrencies. Crypto-CFDs were banned outright for UK retail clients on 6 January 2021 under PS20/10. Before these caps, UK retail traders could routinely access 500:1 leverage on major FX and around 50:1 on single-stock CFDs.
What that prevents. The FCA estimates its 2019 leverage caps and negative balance protection rules (which apply to retail clients) prevent between £267 million and £451 million of UK retail consumer harm every year. The vast majority of that figure (£259m–£443m) comes from the leverage caps themselves; negative balance protection adds about £6m. In a three-month ESMA temporary ban window before the FCA made the rules permanent, UK retail loss reduction was measured at £77m.
What it doesn't change. CFDs remain a high-loss-rate product. The standard FCA-mandated risk warning each broker on this page displays comes from rolling 12-month firm-specific data, and the disclosed rates across the six brokers reviewed here range from 62% (Capital.com) to 73% (Pepperstone). Lower leverage reduces the size of typical losses, not the frequency. Treat the disclosure number as a floor, not a ceiling.
Source: FCA PS19/18 (1 July 2019) · FCA PS20/10 (6 October 2020)
Platforms That Didn't Make the Cut
We tested more platforms than made this list. The six above earned their place through our scoring methodology. The ones below fell short in one or more weighted categories, though several came close.
- Trading 212, funded since 2024: clean fee structure (zero commission, zero platform fee, fractional shares, in-app ISA), but research and education are thin compared with IG or CMC. Narrowly missed the six.
- Hargreaves Lansdown: the UK's biggest platform by client numbers and the best customer service we encountered, but £11.95 per share trade and a 0.45% fund platform fee priced it out on cost.
- Interactive Brokers: the most capable platform we tested (150+ markets, options, futures, bonds), let down by a dated Trader Workstation interface and a steep learning curve at sub-£50,000 portfolio sizes.
- eToro: CopyTrader and fractional shares from $10 make it beginner-friendly, but the 0.5% FX fee on every GBP deposit and the $5 withdrawal fee drag down value.
For MT4 and MT5 users who want a multi-asset broker with competitive costs, Admiral Markets is another option we've tested. See our full Admiral Markets review for the breakdown. If your needs lean more toward long-term investing than active trading, several of these platforms may suit you better than the CFD-focused brokers in our main list. Our best investment platforms UK guide covers that angle in more detail.
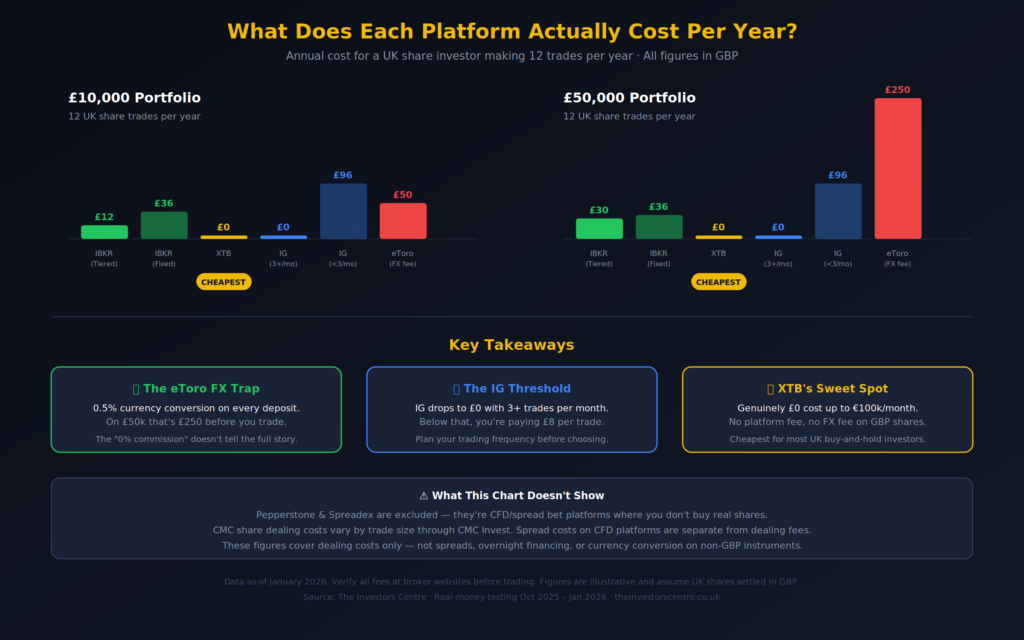
Do Fees Really Make That Much Difference?
Yes. More than most people realise, and in ways that aren’t obvious until you sit down with a calculator, as the scenarios in the table below show.
But here’s what matters more than any single line item: a £3 saving per trade is meaningless if the platform’s execution quality costs you 2 pips in slippage. A 0% commission platform that charges 0.5% on FX conversion costs more than a £5-per-trade platform if you’re buying US stocks every month. Fees are a system, not a number. We’ve broken this down further in our cheapest online broker comparison, and for forex-specific costs, our lowest spread forex brokers guide.
Annual Cost Comparison by Scenario
| Scenario | IG (3+/mo) | IG (<3/mo) | CMC | IBKR (Tiered) | IBKR (Fixed) | eToro |
|---|---|---|---|---|---|---|
| £10k, 12 UK trades/yr | £0 | £96 | Varies | £12 | £36 | £50 (FX) |
| £50k, 12 UK trades/yr | £0 | £96 | Varies | £30 | £36 | £250 (FX) |
Illustrative. Assumes UK shares settled in GBP. eToro cost reflects 0.5% FX on initial deposit. Verify all fees at broker websites. Spreadex and Pepperstone not included in this as its specific to investing.
What Type of Account Should You Actually Open?
The account type you choose matters more than which broker you pick.
A General Investment Account (GIA) has no limits and full flexibility, but profits above the £3,000 annual exemption (2025/26 tax year) are subject to Capital Gains Tax. A Stocks and Shares ISA allows up to £20,000 per tax year, with all gains and dividends completely tax-free. We compare ISA-offering platforms in our best investment platforms guide. A SIPP (Self-Invested Personal Pension) offers tax-free growth plus tax relief on contributions, but your money is locked until age 55, rising to 57 from April 2028.
Account Type Availability
| Platform | GIA | Stocks & Shares ISA | SIPP |
|---|---|---|---|
| IG | Yes | Yes | Yes |
| Pepperstone | CFD account only | No | No |
| Spreadex | Spread bet & CFD account only | No | No |
| Capital.com | Yes | Yes | No |
| CMC Markets | Yes | Yes (CMC Invest) | No |
| Saxo | Yes | Yes | Yes |
What Tax Will You Pay When You Trade?
Stamp Duty Reserve Tax (SDRT): 0.5% on UK share purchases settled electronically through CREST. It’s automatically deducted by your broker. You won’t see a separate charge, but it’s built into the transaction. SDRT doesn’t apply to CFDs, spread bets, ETFs traded on overseas exchanges, or AIM-listed shares. If you’re on Pepperstone or Spreadex, you’ll never encounter this because you never own the underlying asset.
Capital Gains Tax (CGT): 18% for basic-rate taxpayers and 24% for higher-rate taxpayers on gains above the £3,000 annual exemption (2025/26 tax year). This does not apply to gains inside an ISA or SIPP, which is precisely why the account type table above matters so much.
Dividend Tax: 8.75% (basic rate), 33.75% (higher rate), and 39.35% (additional rate) on dividend income above the £500 annual allowance (2025/26). From April 2026, basic and higher rates are scheduled to rise to 10.75% and 35.75% respectively [verify against latest Finance Act before publication]. Again, none of this applies inside an ISA. This is why the ISA column keeps coming up, and why our investing hub focuses heavily on tax-efficient wrappers.
Spread betting: Profits are currently tax-free under HMRC rules for speculators. But, and this is important: if HMRC decides trading is your primary income source, the exemption may not apply. Get professional advice if this is relevant to your situation.
Sources: HMRC CGT rates (gov.uk) · FSCS (fscs.org.uk)
Is Your Money Safe if a Broker Goes Bust?
Every platform on this list is FCA-authorised, which means client funds are held in segregated accounts separate from the broker’s own money. On top of that, the Financial Services Compensation Scheme (FSCS) covers up to £85,000 per eligible person per firm for investment claims if a broker fails financially. You can verify any broker’s authorisation at register.fca.org.uk, and I’ve included the FRN for each broker in its fact table above. If those numbers aren’t on the register, don’t use the platform.
The nuance most people miss: FSCS protects you if the broker goes bust, not against market losses. Being FCA-regulated makes a broker safer to hold your money with; it does not make trading itself safe. If your shares fall in value, that’s your risk; if you trade CFDs, those are leveraged products that carry a high risk of losing money regardless of how well-regulated the broker is. FSCS only covers a broker failing and a shortfall on your segregated funds, up to £85,000. Regulation is one of the core criteria in how we test every platform, and you can read more on our corporate governance page.
Final Thoughts
Most people reading this will be better served by two platforms rather than one: a trading account for short-term positions and an ISA for long-term holdings. That’s exactly what I do, pairing Capital.com for combined trading and investing with Pepperstone when execution speed matters. The platforms on this list are all FCA-regulated, all funded by us with real money, and all worth your time. The risk is real, the rankings are guidance, and the FCA register is your final check before depositing a penny.
FAQs
The questions below are real questions our readers and the wider UK finance community ask, sourced from the TIC Community, relevant Reddit threads, and the People Also Ask data we monitor for each topic. We answer them in the order they're most commonly raised.
Which platform is best for day trading in the UK?
Pepperstone for forex and indices, execution speed is its core advantage, and I’ve consistently recorded fills under 40ms during high-volatility sessions. IG for equities, the Level 2 order book via ProRealTime gives you depth-of-market data that most retail platforms don’t offer. If you want a tax advantage, spread betting on either Spreadex or IG means profits are currently CGT-exempt under HMRC rules. For a full breakdown, see our best day trading platforms guide.
What is the 7% rule in stock trading?
It’s a risk management principle from William O’Neil’s CAN SLIM methodology: sell if a position falls 7% below your purchase price to cap losses. Whether it’s useful depends on your timeframe. For a buy-and-hold investor in an ISA, a 7% dip in a diversified portfolio is routine and shouldn’t trigger panic selling. For a leveraged CFD trader, 7% of the notional position could mean substantially more than 7% of your actual capital. I use stop-losses on every CFD trade, but I don’t apply a blanket 7% rule to my ISA holdings.
What happens to my shares if my broker goes bust?
If you hold real shares, not CFDs, you own the underlying asset. In administration, those shares should be identifiable, ring-fenced, and transferable to another broker. The process takes time, but the asset is legally yours. CFD positions are different: they’d likely be closed at prevailing market prices during the administration process. FSCS covers up to £85,000 per person if there’s a shortfall between what you’re owed and what the administrator can return.
References
- IG Group – Share Dealing and Trading
- CMC Markets – Next-Generation Trading Platform
- Spreadex – Spread Betting and CFDs
- Capital.com – Trading and Investing
- Saxo – SaxoTrader UK Platform
- Pepperstone – Pepperstone UK
- FCA Register – Financial Services Register
- Trustpilot – Trustpilot UK
Other equity trading articles
Cheapest online broker in the UK
Lowest per-trade fees and FX charges.
Read moreHigh-volume share dealing brokers
Tiered pricing for active traders.
Read moreReading chart patterns on shares
Triangles, flags and head & shoulders in practice.
Read moreTop UK day trading platforms
Built for active intraday execution.
Read moreTop AI trading bots
Hosted automation ranked for UK traders.
Read moreFree trading courses for UK traders
Where to learn without paying.
Read more61% of Retail CFD Accounts Lose Money
