How to Buy Cryptocurrency In The UK (2026 Guide)

- expertise:
- CFD Trading, Forex, Derivatives, Risk Management
- credentials:
- Chartered ACII (2018) · Trading since 2012
- tested:
- 40+ forex & CFD platforms with live accounts

- expertise:
- Broker Comparison, ISA Strategy, Portfolio Management
- credentials:
- Active investor since 2013 · 11+ years experience
- tested:
- 40+ brokers with funded accounts
How We Test
Real accounts. Real money. Real trades. No demo accounts or press releases.
What we measure:
- Spreads vs advertised rates
- Execution speed and slippage
- Hidden fees (overnight, withdrawal, conversion)
- Actual withdrawal times
Scoring:
Fees (25%) · Platform (20%) · Assets (15%) · Mobile (15%) · Tools (10%) · Support (10%) · Regulation (5%)
Regulatory checks:
FCA Register verification · FSCS protection
Testing team:
Adam Woodhead (investing since 2013), Thomas Drury (Chartered ACII, 2018), Dom Farnell (investing since 2013) — 50+ platforms with funded accounts
Quarterly reviews · Corrections: info@theinvestorscentre.co.uk
Disclaimer
Not financial advice. Educational content only. We're not FCA authorised. Consult a qualified advisor before investing.
Capital at risk. Investments can fall. Past performance doesn't guarantee future results.
CFD warning. 67-84% of retail accounts lose money trading CFDs. High risk due to leverage.
Contact: info@theinvestorscentre.co.uk
Quick Answer: How to Buy Crypto in the UK
To buy cryptocurrency in the UK, sign up for an FCA-registered exchange (such as Coinbase, eToro, or IG), complete KYC verification with a valid ID, deposit GBP via bank transfer or debit card, and place your order.
Note: Some UK banks restrict crypto transactions. Using crypto-friendly banks or services like Revolut can reduce issues. The FCA warns crypto is high-risk -- only invest what you can afford to lose.
Key Steps to Buy Crypto in the UK
- Choose a Platform: Use FCA-registered, UK-compliant platforms like Coinbase, eToro, Bitpanda, or Revolut for easy GBP deposits.
- Verify Identity (KYC): Provide ID such as a passport or driving licence for anti-money laundering compliance.
- Deposit Funds: Add GBP via bank transfer (faster/cheaper) or debit card.
- Buy Crypto: Search for your chosen cryptocurrency and purchase a fraction or whole coin.
- Secure Your Assets: Use a private wallet for long-term storage or keep on the exchange for trading.
Buying crypto in the UK is easier than ever -- but picking the right platform matters. This 2026 guide walks you through the full process, from choosing an exchange to storing your coins safely.
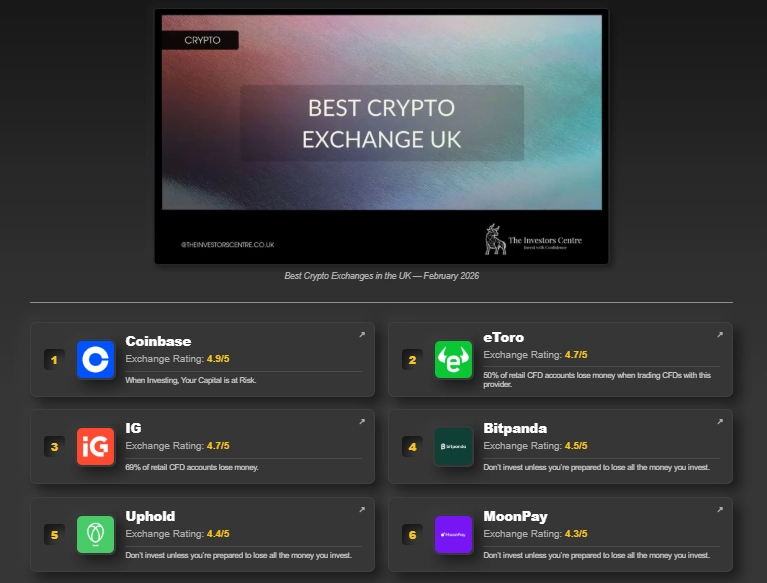
Top 4 Exchanges
| Rank | Platform | Crypto Score | Risk Warning |
|---|---|---|---|
| 1 | Coinbase | 4.9/5 | Investing in crypto carries a high level of risk. |
| 2 | eToro | 4.7/5 | 61% of retail CFD accounts lose money. |
| 3 | IG | 4.5/5 | Don't invest unless you're prepared to lose all the money you invest. |
| 4 | Bitpanda | 4.5/5 | Don't invest unless you're prepared to lose all the money you invest. |
How Can You Buy Cryptocurrency in the UK? (Step-by-Step)
Step 1 -- Choosing a Crypto Exchange or Broker
Start by selecting a platform that's FCA-registered, has low fees, a user-friendly interface, and strong security features. Consider reputation, available coins, and ease of withdrawals. Popular UK options include Bitpanda, eToro, Coinbase, and Kraken -- see our full ranking of the best crypto exchanges in the UK for a detailed comparison. If you'd rather trade from your phone, we've also tested the best crypto apps in the UK.
What's the Difference Between a Crypto Exchange and a Broker?
A crypto exchange lets you trade directly with other users and often has more coins and advanced features. A broker, on the other hand, simplifies buying by setting prices for you -- ideal for beginners who want quick, easy purchases without market complexity.
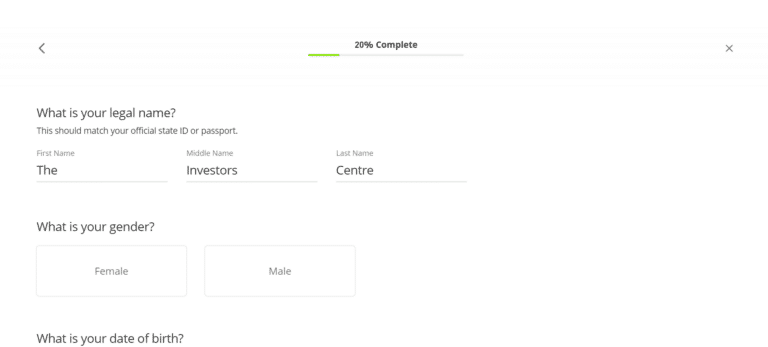
Step 2 -- Registering and Verifying Your Identity
Once you've chosen a platform, create an account using your email and a strong password. Next, complete identity verification by submitting proof of ID (passport or driver's licence) and address (utility bill or bank statement). This step ensures compliance with UK regulations.
What's Involved in the KYC (Know Your Customer) Process?
KYC involves uploading identification documents, taking a selfie for facial recognition, and verifying your address. Most UK platforms complete this within minutes to a few hours. It's a legal requirement designed to prevent fraud, money laundering, and ensure platform security for all users.
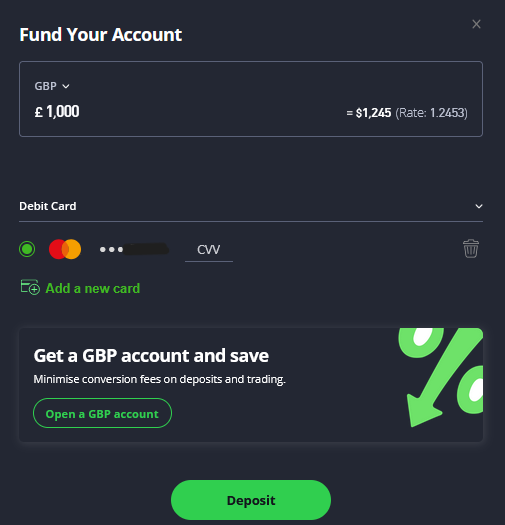
Step 3 -- Depositing Funds Into Your Account
To fund your account, log in to your chosen platform and head to the "Deposit" or "Add Funds" section. Most UK exchanges accept bank transfers, debit cards, or e-wallets like PayPal. Choose your method, enter the amount, and follow the on-screen instructions. Some UK banks block crypto transactions -- if yours does, check our list of crypto-friendly banks in the UK.
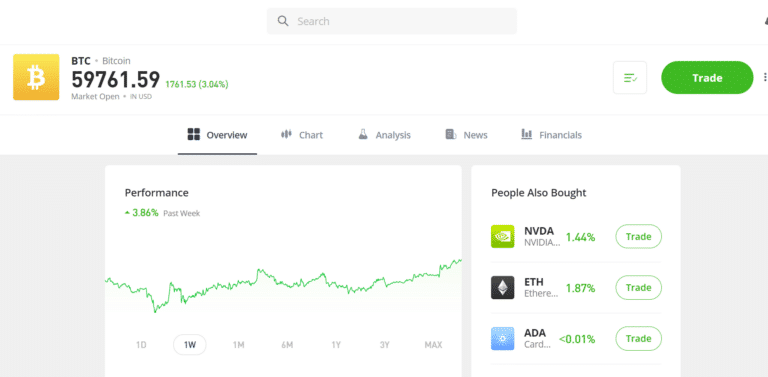
Step 4 -- Placing Your First Crypto Order
After funding your account, go to the platform's "Buy" section. Select the cryptocurrency you want -- whether that's Bitcoin , Ethereum (ETH), or an altcoin like Solana or XRP -- enter the amount you wish to buy, and confirm the order. Most platforms offer one-click purchases for beginners and advanced options for experienced traders.
Step 5: Secure Your Crypto Assets
After purchasing crypto, it's crucial to protect it. Most platforms store your assets by default, but moving them to a private wallet adds extra security -- especially against exchange hacks. Choose between a software wallet (app-based) or a hardware wallet (offline physical device).
Should You Store Your Crypto on an Exchange or in a Wallet?
Storing crypto on an exchange is convenient but riskier long-term. Wallets give you full control and stronger protection. For large amounts or long-term holding, a private wallet -- especially a hardware one -- is the safer choice.
| Storage Option | Pros | Cons | Security Level |
|---|---|---|---|
| Exchange | Easy access, convenient for trading | Higher risk of hacks | Moderate (with 2FA) |
| Private Wallet | Greater control, enhanced security | Less convenient for frequent trades | High (especially with cold storage) |
Are There Alternative Ways to Buy Crypto in the UK?
Yes, you can also buy crypto using Bitcoin ATMs, peer-to-peer platforms like Paxful, or even via fintech apps like Revolut. However, these may come with higher fees, limited coin options, or fewer security features compared to dedicated crypto platforms.
What Should You Know Before Investing in Cryptocurrency?
Cryptocurrency can be an exciting and potentially profitable investment -- but it also carries significant risks. Before you dive in, it's essential to understand how crypto works, what influences its value, and the legal and tax responsibilities you have as a UK investor.
What Is Cryptocurrency and How Does It Work?
Cryptocurrency is a digital form of money that operates on a technology called blockchain -- a secure, decentralised ledger that records transactions across a network. Instead of being issued by a central bank, crypto coins and tokens like Bitcoin or Ethereum are maintained by users and miners. These assets can be used for payments, trading, or held as investments.
What Key Factors Should You Consider When Buying Cryptocurrency?
- Volatility: Prices can rise or fall dramatically within hours. Only invest what you can afford to lose.
- Market Timing: Crypto is driven by hype cycles, news, and investor sentiment. Timing matters. If you want a starting point, see our analysts' picks for the best crypto to invest in right now.
- Research: Understand what each coin does. Is it solving a problem, or just speculative?
- Regulation: Regulatory news can affect prices overnight. Stay informed.
- Security: Make sure your crypto is stored safely. Consider wallets over exchanges for long-term holding.
- Scams and Hype: Be wary of "get rich quick" schemes or anonymous coins with no clear purpose.
Is Buying Cryptocurrency Legal in the UK?
Yes, buying and owning cryptocurrency is legal in the UK. The Financial Conduct Authority (FCA) regulates firms offering crypto-related services, especially if they involve fiat on/off ramps or custody. However, crypto itself is not classified as legal tender and is not protected by the Financial Services Compensation Scheme (FSCS). Always use FCA-registered platforms to ensure compliance and safety. For a full breakdown of UK crypto law, see our guide: is Bitcoin legal in the UK.
Do You Have to Pay Taxes on Crypto in the UK?
Yes, cryptocurrency is subject to capital gains tax (CGT) in the UK. If you sell crypto for a profit, swap one coin for another, or use it to make purchases, you may owe tax. HMRC requires individuals to keep detailed records and report gains on their annual self-assessment. In some cases, frequent trading may be taxed as income. Using tools like Koinly or CoinTracker can help you stay compliant.
For context, check our regularly updated UK crypto statistics 2026 page covering ownership, demographics, and market trends.
Which Crypto Platforms Are FCA-Registered in the UK?
Choosing the right platform is crucial for a smooth, safe crypto investing experience. UK users benefit from several reputable, FCA-registered platforms offering different strengths -- from low fees to user-friendly interfaces.
Which Platforms Are Most Trusted by UK Users?
- Bitpanda: FCA-registered with the UK's largest crypto selection (600+ assets), zero deposit fees, and enterprise-grade security. Ideal for beginners and low-cap hunters alike.
- eToro: FCA-registered with strong copy-trading features, a simple interface, and built-in wallet. Great for beginners.
- Coinbase: Known for ease of use, good customer support, and strong compliance. Slightly higher fees.
- IG: FTSE 250-listed platform with 1.49% flat fees, real crypto ownership across 55+ coins, and unified multi-asset trading. Best for buy-and-hold investors wanting simplicity.
- Kraken: Highly secure, with solid regulatory standing and advanced tools for experienced traders.
How Do the Leading UK Platforms Compare?
| Rank | Platform | Min Deposit | FCA Registered? | Platforms | Best For |
|---|---|---|---|---|---|
| 1 | Coinbase | £0 | Yes | Web, mobile | Beginner-friendly with strong compliance |
| 2 | eToro | £40 | Yes | Web, mobile | Social/copy trading beginners |
| 3 | IG | £1 | Yes | Web, mobile | Low-fee traders and multi-asset investors |
| 4 | Bitpanda | £1 | Yes | Web, mobile | Low-cap crypto hunters and beginners |
| 5 | Kraken | £0 | Yes | Web, desktop, mobile | Advanced traders and staking users |
What's Changed in 2026?
FCA-registered platforms like Coinbase and eToro remain the safest starting point for UK buyers. Crypto ETNs are now available on the London Stock Exchange, offering a regulated route into Bitcoin and Ethereum. Bitpanda has expanded its UK presence with competitive fees and a huge asset range. Tighter FCA marketing rules have made it easier to spot legitimate exchanges. Overall, it's become simpler to buy crypto legally -- but the volatility and risks haven't changed.
If you are looking to go beyond spot buying and want to understand how leverage works for UK crypto investors, Bitpanda's spot margin product is currently the only FCA-registered retail option available. Our guide to crypto leverage platforms in the UK covers the full landscape, and our step-by-step crypto leverage trading guide documents the process — including a live trade completed in March 2026.
UK Bank Restrictions When Buying Crypto
Some UK banks restrict or block transactions to cryptocurrency exchanges. Banks including Santander, HSBC, and NatWest have previously blocked payments to certain crypto platforms.
How to Avoid Bank Blocks
- Use crypto-friendly banks: Monzo, Starling, and Revolut generally allow crypto purchases
- Try bank transfers instead of cards: Card payments are more likely to be blocked than Faster Payments
- Use platforms with UK banking relationships: Coinbase, eToro, and Bitpanda have established UK banking partnerships
Tip: If your bank blocks a transaction, contact them to whitelist the exchange or consider opening a secondary account with a crypto-friendly provider.
Final Thoughts: Is Now the Right Time to Buy Crypto in the UK?
Crypto isn't going anywhere, but that doesn't mean it's risk-free. Start with a regulated platform, stick to coins you actually understand, and never invest more than you can afford to lose. Keep your assets secure -- whether that's on a trusted exchange or in your own wallet. Do your own research, stay patient, and treat crypto as one piece of a wider investment strategy.
Looking for specific coin guides? We've written step-by-step buying instructions for buying Solana in the UK, how to buy XRP, buying Dogecoin (DOGE), and more. And if fees are a priority, our comparison of crypto platforms with the lowest fees will help you keep costs down.
Top 5 Exchanges
| Rank | Platform | Risk Warning |
|---|---|---|
| 1 | Coinbase | Investing in crypto carries a high level of risk. |
| 2 | eToro | Investing in crypto carries a high level of risk. |
| 3 | IG | Don't invest unless you're prepared to lose all the money you invest. |
| 4 | Bitpanda | Don't invest unless you're prepared to lose all the money you invest. |
| 5 | Kraken | Investing in crypto carries a high level of risk. |
FAQs
Is it legal to buy crypto in the UK?
Yes, buying and owning cryptocurrency is completely legal in the UK. The Financial Conduct Authority (FCA) regulates crypto marketing and requires exchanges to register before serving UK customers. However, crypto is classified as a high-risk investment and is not protected by the Financial Services Compensation Scheme (FSCS). The FCA advises that you should only invest money you can afford to lose entirely.
What is the best platform to buy cryptocurrency in the UK?
The best FCA-registered platforms for buying crypto in the UK include Coinbase, eToro, IG, Bitpanda, and Kraken. Coinbase is ideal for beginners due to its simple interface. eToro offers copy trading features. Bitpanda has the widest selection of cryptocurrencies (600+). Kraken suits advanced traders with lower fees. Choose based on your experience level, preferred coins, and fee tolerance.
Do UK banks allow crypto purchases?
Some UK banks restrict or block transactions to cryptocurrency exchanges. Banks including Santander, HSBC, and NatWest have blocked payments to certain platforms. Crypto-friendly alternatives include Monzo, Starling, and Revolut, which generally allow crypto purchases without restrictions. Using bank transfers (Faster Payments) instead of debit cards can also help avoid blocks, as card payments are more frequently declined.
How much should I invest in cryptocurrency as a beginner?
As a beginner, start with a small amount you can afford to lose entirely -- most experts suggest no more than 5-10% of your investment portfolio. Many UK platforms allow purchases from as little as £10. The cryptocurrency market is highly volatile, so starting small helps you learn market dynamics without risking significant savings. Never invest emergency funds, borrowed money, or money needed for essential expenses.
What payment methods can I use to buy crypto in the UK?
UK residents can buy cryptocurrency using bank transfers (Faster Payments), debit cards, credit cards (limited availability), and e-wallets like PayPal. Bank transfers are typically free or low-cost and process within hours. Debit card purchases are instant but often carry 1-3% fees. Most FCA-registered exchanges accept GBP deposits directly, avoiding currency conversion charges.
How do I cash out cryptocurrency in the UK?
To cash out crypto in the UK, sell your cryptocurrency for GBP on your exchange, then withdraw to your UK bank account. Most platforms process GBP withdrawals via Faster Payments within 24 hours. Be aware of withdrawal fees (typically £0-£2) and potential capital gains tax obligations if you've made a profit exceeding the annual CGT allowance (£3,000 for 2025/26).
Do I have to pay tax on cryptocurrency in the UK?
Yes, cryptocurrency is subject to Capital Gains Tax (CGT) in the UK. You must pay CGT on profits when you sell crypto, swap one cryptocurrency for another, or use crypto to purchase goods/services. The tax-free allowance is £3,000 for 2025/26. Gains above this are taxed at 18% (basic rate) or 24% (higher rate). HMRC requires you to keep records of all transactions and report gains on your Self Assessment tax return.
What is KYC and why do crypto exchanges require it?
KYC (Know Your Customer) is identity verification required by FCA-registered crypto exchanges to comply with anti-money laundering regulations. You'll need to provide a government-issued ID (passport or driving licence), proof of address, and sometimes a selfie for facial recognition. Most UK platforms complete KYC verification within minutes to a few hours. Without completing KYC, you cannot deposit GBP or withdraw funds.
Should I store crypto on an exchange or in a wallet?
For small amounts or active trading, keeping crypto on a reputable FCA-registered exchange with 2FA enabled is convenient and reasonably secure. For larger holdings or long-term storage, transfer to a private hardware wallet (like Ledger or Trezor) for maximum security -- you control the private keys. The crypto saying "not your keys, not your coins" reflects the risk that exchanges can be hacked or go bankrupt, as seen with FTX in 2022.
How long does it take to buy cryptocurrency in the UK?
You can complete your first crypto purchase within 10-30 minutes if using a debit card on platforms like Coinbase or eToro. The process involves: creating an account (2 minutes), completing KYC verification (5-15 minutes), depositing funds (instant with card, 1-24 hours via bank transfer), and placing your order (1 minute). Bank transfers take longer but have lower fees.
References
- FCA (Financial Conduct Authority) -- Cryptoasset consumer research
- Bank of England -- What are cryptoassets?
- Coinbase UK -- How to buy crypto in the UK (official guide)
- HMRC -- Cryptoassets: tax for individuals
- eToro UK -- Guide to crypto trading and investing
- CoinTelegraph -- How to buy Bitcoin and Ethereum in the UK
- Forbes -- Get Started In Investing In Cryptocurrency
- BBC News -- Bitcoin: Crypto Fans
- GOV.UK -- Economic Crime and Corporate Transparency act
- ✓ Buy crypto instantly with GBP via bank transfer or card
- ✓ Earn rewards on supported cryptocurrencies
- ✓ Lower fees available through Coinbase Advanced
Don’t invest unless you’re prepared to lose all the money you invest. This is a high-risk investment and you should not expect to be protected if something goes wrong. Take 2 mins to learn more
More crypto how-to guides
How to Buy Dogecoin UK
Step-by-step UK buyer's guide.
Read moreHow to Buy Ethereum UK
Step-by-step UK buyer's guide.
Read moreHow to Buy Kaspa
Step-by-step UK buyer's guide.
Read moreHow to Buy Solana UK
Step-by-step UK buyer's guide.
Read moreHow to Buy XRP UK
Step-by-step UK buyer's guide.
Read moreCrypto
Read our guide.
Read moreWhen Investing, Your Capital is at Risk.
